There comes a time in any person’s life[1] when they realise that they’re not going to be able to do all the things they might like to do to a high level of expertise. I used to kid myself that I could do anything if I tried hard enough and practised enough, but then I tried juggling. It turns out that I’m never going to be able to juggle. Not just juggle expertly. I mean juggle at all. My trying to juggle – with only one ball, let alone more than one – is so amusing that my family realised years ago that it was a great party trick. “Daddy,” they’ll say, “show everyone your juggling. It’s really funny.” “But I can’t juggle,” I retort. “Yes,” they respond, “that’s what’s funny[2].”
I’m also never going to be able to draw or do any art with any competence.
Or play any racquet sport with any level of skill.
Or do any gardening, painting or DIY-based household jobs with any degree of expertise[3].
Some people will retort that any old fool can be taught to do x activity (usually, it’s juggling, actually), but not only do I not believe this, but also, to be honest, there just isn’t enough time in the day to learn all the things I’d kind of like to try.
What has all this to do with security?
Specialism and education
Well, I’ve posted before that I’m a systems person, and the core of thinking about systems is that you need to look at the big picture. In order to do that, you need to be a generalist. There’s a phrase[5] in English: “Jack of all trades, master of none”, which is often used to condemn those who know a little about many things and are seen to dabble in them without a full understanding of any of them. Interestingly, this version may be an abbreviation of the original, more positive:
- Jack of all trades, master of none,
- though oftentimes better than master of one.
The core inference, though, is that generalists aren’t as useful as specialists. I don’t believe this.
In many educational systems, there’s a tendency to push students towards narrower and narrower fields of study. For some, this is just what is needed, but for others – “systems people”, “synthesists” and “generalists” – this isn’t the best way to harness their talents, at least in the long term. We need people who can see the big picture, who can take a wider view, and look beyond a single blocking issue to realise that the answer to a problem may not be a better implementation of an authentication library, but a change in the authorisation mechanism being used at the component level, for instance.
There are dangers to following this approach too far, however:
- it can lead to disparagement of specialists and their skills, even to a distrust of experts;
- it can lead to arrogance on the part of generalists.
We see the first in desperately concerning trends such as politicians thinking they know more than economists or climate scientists, anti-vaxxers ignoring the benefits of vaccination, and idiocy around chem-trails, flat-earth beliefs and moon landing conspiracies. It happens in the world of work, as well, I’m sad to say. There is a particular type of MBA recipient, for instance, who believes that the completion of the course and award of the degree confers on them some sort of superhuman ability to know what is is best for all organisations in all circumstances[6].
Specialise first
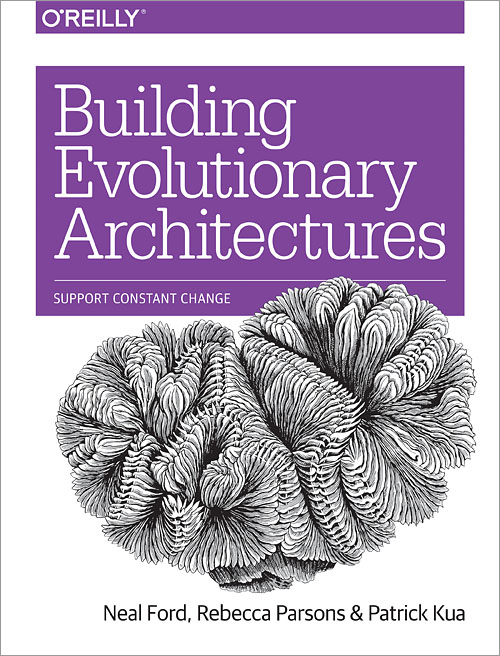
To come back to the world of security, my recommendation is that even if you know that your skills and interests are leading you to a career as a generalist, then you need to become a specialist first, in at least area. You may not become an expert in that field, but you need to know it well. Better still, strive for at least a level of competence in several fields – an ability to converse knowledgeably with true experts and to understand at least why they are making the choices and recommendations that they are.
And that leads us to the key point here: if you become a generalist, you need to acknowledge lack of expertise: it must become your modus operandi, your métier, your way of working. You need to recognise that your strength is not in your knowing many things, but in knowing what you don’t know, and when it is time to call in the specialists.
I’m not a cryptographer, but I know enough about cryptography to realise when it’s time to call in an expert. I’m not an expert on legal issues around cryptography, either, but know when to call on a lawyer. Nor am I an expert on block storage, blockchain consensus, quantum key exchange protocols, CPU scheduling or compression algorithms. The same will go for many areas which I may be called on to touch as part of my job. I hope to have enough training and expertise within related fields – or the ability to gain it – to be able to ask sensible questions, but sometimes even that won’t be true, and the best (and most productive) interaction will be to say “I don’t know about this: please explain it to me, or at least tell me what the options are.” This seems to me to be particularly important for security folks: there are so many overlapping disciplines, and getting one piece wrong means that your defence in depth strategy just got a whole lot shallower.
Being too lazy to look things up, too arrogant to listen to others or too short-sighted to realise that there are areas in which we are not expert are things of which we should be ashamed.
But there is no shame in being a generalist, and knowing when you need to consult a specialist.
1 – I’m extrapolating horribly here, but it’s true for me so I’m assuming it’s a universal truth.
2 – apparently the look on my face, and the things I do with my tongue, are a sight to behold.
3 – I’m constantly trying to convince my wife of these, and although she’s sceptical about some, we’re now agreed that I shouldn’t be allowed access to any power tools again if we want avoid further trips to the Accident and Emergency department at the hospital[4].
4 – it’s not only power tools. I once nearly removed my foot with a wallpaper stripper. I still have the scar nearly 25 years later.
5 – somewhat gendered, for which I apologise.
6 – disclaimer – I have an MBA, and met many talented and humble people on my course (and have met many since) who don’t suffer from this predicament.